Netwerk: verschil tussen versies
Naar navigatie springen
Naar zoeken springen
(Aanvankelijke omzetting naar winkelsteeg) |
Geen bewerkingssamenvatting |
||
| Regel 6: | Regel 6: | ||
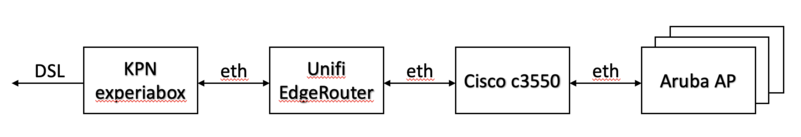
Dit plaatje is verouderd (dit was de setup aan de Villanovastraat). Tegenwoordig is het: | Dit plaatje is verouderd (dit was de setup aan de Villanovastraat). Tegenwoordig is het: | ||
<---Odido (5G)---| Odido router |<---eth--->| | <---Odido (5G)---| Odido router |<---eth--->| pfsense |<---eth--->| Netgear GS728TP |<---eth--->| Aruba APs... | | ||
=TODO= | =TODO= | ||
| Regel 16: | Regel 16: | ||
=VLANs= | =VLANs= | ||
*1 | *1 (of untagged) - management | ||
**dhcp-server op pfsense | **dhcp-server op pfsense | ||
**10.138. | **10.138.1.0/24 | ||
***10.138. | ***10.138.1.1 pfsense | ||
***10.138. | ***10.138.1.2 switch | ||
*1336 - Park Winkelsteeg | *1336 - Park Winkelsteeg | ||
**dhcp-server op pfsense | **dhcp-server op pfsense | ||
| Regel 34: | Regel 32: | ||
=Netgear GS728TP= | =Netgear GS728TP= | ||
*Fixed to 10.138. | *Fixed to 10.138.1.2, untagged | ||
*No IP on all other VLANs | *No IP on all other VLANs | ||
==Ports== | ==Ports== | ||
| Regel 57: | Regel 39: | ||
*1 --> pfsense | *1 --> pfsense | ||
**vlan 1 (untagged) | **vlan 1 (untagged) | ||
**vlan 1336 | **vlan 1336 | ||
**vlan 1337 | **vlan 1337 | ||
*2 --> accesspoint | *2 --> accesspoint in de ruimte met de wc | ||
**vlan 1 (untagged) | **vlan 1 (untagged) | ||
**vlan 1336 | **vlan 1336 | ||
**vlan 1337 | **vlan 1337 | ||
*3 --> accesspoint | *3 --> accesspoint in de ruimte met de keuken | ||
**vlan 1 (untagged) | **vlan 1 (untagged) | ||
**vlan 1336 | **vlan 1336 | ||
**vlan 1337 | **vlan 1337 | ||
*4 --> accesspoint | *4 --> accesspoint Diana 1 | ||
** | **vlan 1 (untagged) | ||
**vlan 1336 | |||
**vlan 1337 | |||
*5 --> accesspoint Diana 2 | |||
**vlan 1 (untagged) | **vlan 1 (untagged) | ||
**vlan 1336 | **vlan 1336 | ||
**vlan 1337 | **vlan 1337 | ||
=pfsense= | =pfsense= | ||
| Regel 89: | Regel 62: | ||
*dhcp servers: | *dhcp servers: | ||
**let erop dat je de pool start/end moet invullen, anders is de pool size 0 en krijg je geen leases | **let erop dat je de pool start/end moet invullen, anders is de pool size 0 en krijg je geen leases | ||
**mgmt 10.138. | **mgmt 10.138.1.0/24 (vanaf .10) | ||
**winkelsteeg 10.138.65.0/24 (vanaf .10) | **winkelsteeg 10.138.65.0/24 (vanaf .10) | ||
**hsn 10.138.66.0/24 (vanaf .10) | **hsn 10.138.66.0/24 (vanaf .10) | ||
*in de config tree: service -> gui -> listen-address "10.138. | *in de config tree: service -> gui -> listen-address "10.138.1.1" zodat ie alleen bereikbaar is via management vlan | ||
==Ports== | ==Ports== | ||
| Regel 99: | Regel 72: | ||
**dhcp client | **dhcp client | ||
*eth1 lan --> netgear port 1 trunkport | *eth1 lan --> netgear port 1 trunkport | ||
**vlan 1 (untagged | **vlan 1 (untagged, management, dhcp-server) | ||
**vlan 1336 (dhcp-server) | **vlan 1336 (dhcp-server) | ||
**vlan 1337 (dhcp-server) | **vlan 1337 (dhcp-server) | ||
*eth2 | *eth2 | ||
**vlan 1 (untagged | **vlan 1 (untagged, management, dhcp-server) | ||
**vlan 1336 (dhcp-server) | **vlan 1336 (dhcp-server) | ||
**vlan 1337 (dhcp-server) | **vlan 1337 (dhcp-server) | ||
*eth3 | *eth3 | ||
**vlan 1 (untagged | **vlan 1 (untagged, management, dhcp-server) | ||
**vlan 1336 (dhcp-server) | **vlan 1336 (dhcp-server) | ||
**vlan 1337 (dhcp-server) | **vlan 1337 (dhcp-server) | ||
*eth4 | *eth4 | ||
**vlan 1 (untagged | **vlan 1 (untagged, management, dhcp-server) | ||
**vlan 1336 (dhcp-server) | **vlan 1336 (dhcp-server) | ||
**vlan 1337 (dhcp-server) | **vlan 1337 (dhcp-server) | ||
== Firewall == | == Firewall == | ||
Reject traffic from guest VLANs ( | Reject traffic from guest VLANs (winkelsteeg) to management VLAN: | ||
* Firewall/NAT -> Firewall/NAT Groups -> create "management" group, then Actions -> Config and set network "10.138.64.0/24" and save | * Firewall/NAT -> Firewall/NAT Groups -> create "management" group, then Actions -> Config and set network "10.138.64.0/24" and save | ||
* Firewall Policies -> Add ruleset "GUEST_NET_LOCAL" : | * Firewall Policies -> Add ruleset "GUEST_NET_LOCAL": | ||
** Description "Guest to router" | ** Description "Guest to router" | ||
** Default action DROP | ** Default action DROP | ||
| Regel 130: | Regel 99: | ||
** go to Interfaces and add switch0.1336 direction local, and switch0.1337 direction local | ** go to Interfaces and add switch0.1336 direction local, and switch0.1337 direction local | ||
* Firewall Policies -> Add ruleset "GUEST_NET_IN" | * Firewall Policies -> Add ruleset "GUEST_NET_IN" | ||
** Description "From | ** Description "From guest nets" | ||
** Default action ACCEPT | ** Default action ACCEPT | ||
** add rule 1 "drop guestnet to mgmt" action Drop protocol All protocols destination network group Management subnet | ** add rule 1 "drop guestnet to mgmt" action Drop protocol All protocols destination network group Management subnet | ||
** go to Interfaces and add switch0.1336 direction In, and switch0.1337 direction In | ** go to Interfaces and add switch0.1336 direction In, and switch0.1337 direction In | ||
Now, hosts on | Now, hosts on guest nets can use DHCP and DNS, but nothing else on the router; also, they can't access the management subnet at all. | ||
=Aruba Accesspoints= | =Aruba Accesspoints= | ||
| Regel 141: | Regel 110: | ||
==Setup== | ==Setup== | ||
* | *kies een poortje, zet in de tabel hierboven, hang AP eraan | ||
*default AP config is untagged management, dus AP krijgt automatisch een lease in het management subnet | |||
* | *AP vindt automatisch de huidige instant controller en trekt config daaruit | ||
* | |||
==Individuele settings== | ==Individuele settings== | ||
Versie van 28 mrt 2026 13:13
Deze pagina omschrijft de netwerkinfrastructuur aan de Winkelsteegseweg.
Overview
Dit plaatje is verouderd (dit was de setup aan de Villanovastraat). Tegenwoordig is het:
<---Odido (5G)---| Odido router |<---eth--->| pfsense |<---eth--->| Netgear GS728TP |<---eth--->| Aruba APs... |
TODO
- Backup configs
- Note passwords somewhere outside of this wiki
- Spacenet
VLANs
- 1 (of untagged) - management
- dhcp-server op pfsense
- 10.138.1.0/24
- 10.138.1.1 pfsense
- 10.138.1.2 switch
- 1336 - Park Winkelsteeg
- dhcp-server op pfsense
- 10.138.65.0/24
- 10.138.65.1 pfsense
- 1337 - hsn
- dhcp-server op pfsense
- 10.138.66.0/24
- 10.138.66.1 pfsense
Netgear GS728TP
- Fixed to 10.138.1.2, untagged
- No IP on all other VLANs
Ports
- 1 --> pfsense
- vlan 1 (untagged)
- vlan 1336
- vlan 1337
- 2 --> accesspoint in de ruimte met de wc
- vlan 1 (untagged)
- vlan 1336
- vlan 1337
- 3 --> accesspoint in de ruimte met de keuken
- vlan 1 (untagged)
- vlan 1336
- vlan 1337
- 4 --> accesspoint Diana 1
- vlan 1 (untagged)
- vlan 1336
- vlan 1337
- 5 --> accesspoint Diana 2
- vlan 1 (untagged)
- vlan 1336
- vlan 1337
pfsense
- dhcp servers:
- let erop dat je de pool start/end moet invullen, anders is de pool size 0 en krijg je geen leases
- mgmt 10.138.1.0/24 (vanaf .10)
- winkelsteeg 10.138.65.0/24 (vanaf .10)
- hsn 10.138.66.0/24 (vanaf .10)
- in de config tree: service -> gui -> listen-address "10.138.1.1" zodat ie alleen bereikbaar is via management vlan
Ports
- eth0 wan --> Odido-router
- dhcp client
- eth1 lan --> netgear port 1 trunkport
- vlan 1 (untagged, management, dhcp-server)
- vlan 1336 (dhcp-server)
- vlan 1337 (dhcp-server)
- eth2
- vlan 1 (untagged, management, dhcp-server)
- vlan 1336 (dhcp-server)
- vlan 1337 (dhcp-server)
- eth3
- vlan 1 (untagged, management, dhcp-server)
- vlan 1336 (dhcp-server)
- vlan 1337 (dhcp-server)
- eth4
- vlan 1 (untagged, management, dhcp-server)
- vlan 1336 (dhcp-server)
- vlan 1337 (dhcp-server)
Firewall
Reject traffic from guest VLANs (winkelsteeg) to management VLAN:
- Firewall/NAT -> Firewall/NAT Groups -> create "management" group, then Actions -> Config and set network "10.138.64.0/24" and save
- Firewall Policies -> Add ruleset "GUEST_NET_LOCAL":
- Description "Guest to router"
- Default action DROP
- add rule 1 "allow DNS" action Accept protocol TCP+UDP destination port 53
- add rule 2 "allow DHCP" action Accept protocol UDP destination port 67
- go to Interfaces and add switch0.1336 direction local, and switch0.1337 direction local
- Firewall Policies -> Add ruleset "GUEST_NET_IN"
- Description "From guest nets"
- Default action ACCEPT
- add rule 1 "drop guestnet to mgmt" action Drop protocol All protocols destination network group Management subnet
- go to Interfaces and add switch0.1336 direction In, and switch0.1337 direction In
Now, hosts on guest nets can use DHCP and DNS, but nothing else on the router; also, they can't access the management subnet at all.
Aruba Accesspoints
Setup
- kies een poortje, zet in de tabel hierboven, hang AP eraan
- default AP config is untagged management, dus AP krijgt automatisch een lease in het management subnet
- AP vindt automatisch de huidige instant controller en trekt config daaruit
Individuele settings
Op de controller zijn alle APs online. Maak een nieuw wired network genaamd "passthrough" met:
- Primary usage employee
- PoE enabled
- Admin status Up
- Mode Access
- Client IP Network Assigned
- Access VLAN 1336 (villanova)
- VLAN Assignment Rule "If AP-Name equals AP233 assign VLAN 1337" (AP233 is de accesspoint waar de netwerkkabel naar ons atelier doorheen lust)
Stel "passthrough" in op alle wired poortjes behalve 0/0 (die blijft op default_wired_port_profile).